Winbind/Expired password: различия между версиями
| Строка 44: | Строка 44: | ||
<syntaxhighlight lang="text"># rpcclient -c "lookupnames ex_test4" -P c253.test.alt | sed 's/^.*-\([0-9]\+\) .*$/\1/' | <syntaxhighlight lang="text"># rpcclient -c "lookupnames ex_test4" -P c253.test.alt | sed 's/^.*-\([0-9]\+\) .*$/\1/' | ||
1233 | 1233 | ||
# rpcclient -c "queryuser 1233" -P c253.test.alt | grep -E 'User Name|Password must change Time' | # rpcclient -c "queryuser 1233" -P c253.test.alt | grep -E 'User Name|Password must change Time' | ||
User Name : ex_test4 | |||
Password must change Time: Вс, 03 дек 2023 16:11:12 MSK</syntaxhighlight> | Password must change Time: Вс, 03 дек 2023 16:11:12 MSK</syntaxhighlight> | ||
Версия от 22:40, 26 января 2024
Настройка и отладка реакции на устаревание пароля пользователя в Active Directory для машины, введённой в Active Directory через winbind.
Проверка среды
В качестве примера используется система Альт Рабочая станция 10.1, полностью обновлённая на 26 января 2024 года.
Установка:
apt-get install task-auth-ad-winbind
Проверка версии пакета:
# rpm -q samba-winbind samba-winbind-4.17.12-alt4.x86_64
Внимание! Полноценная смена пароля при устаревании доступна с samba-winbind-4.17.
Проверка устаревания пароля на сервере
# samba-tool user create ex_test4
New Password:
Retype Password:
User 'ex_test4' added successfully
Создаём и применяем PSO для пользователя:
# samba-tool domain passwordsettings pso create 1day_expired 1 --max-pwd-age=2 --min-pwd-age=1
Not all password policy options have been specified.
For unspecified options, the current domain password settings will be used as the default values.
PSO successfully created: CN=1day_expired,CN=Password Settings Container,CN=System,DC=test,DC=alt
Password information for PSO '1day_expired'
Precedence (lowest is best): 1
Password complexity: off
Store plaintext passwords: off
Password history length: 24
Minimum password length: 1
Minimum password age (days): 1
Maximum password age (days): 2
Account lockout duration (mins): 30
Account lockout threshold (attempts): 3
Reset account lockout after (mins): 30
# samba-tool domain passwordsettings pso apply 1day_expired ex_test4
PSO '1day_expired' applied to 'ex_test4'
Проверяем дату устаревания пароля для пользователя ex_test4:
# rpcclient -c "lookupnames ex_test4" -P c253.test.alt | sed 's/^.*-\([0-9]\+\) .*$/\1/'
1233
# rpcclient -c "queryuser 1233" -P c253.test.alt | grep -E 'User Name|Password must change Time'
User Name : ex_test4
Password must change Time: Вс, 03 дек 2023 16:11:12 MSK
Ввод в домен через winbind
# system-auth write ad test.alt host-209 test Administrator 'Pa$$word' --winbind --gpo Using short domain name -- TEST Joined 'HOST-209' to dns domain 'test.alt' DNS update failed!
Настройка pam_winbind
. shell-ini-config export shell_ini_config_prefix= ini_config_set /etc/security/pam_winbind.conf global debug yes ini_config_set /etc/security/pam_winbind.conf global silent no ini_config_set /etc/security/pam_winbind.conf global pwd_change_prompt yes
Проверка содержимого файла:
# grep '^[a-z\[]' /etc/security/pam_winbind.conf
[global]
cached_login = yes
krb5_auth = yes
krb5_ccache_type = KEYRING
silent = no
debug = yes
pwd_change_prompt = yes
После ввода в домен и изменения файла перезагрузите компьютер.
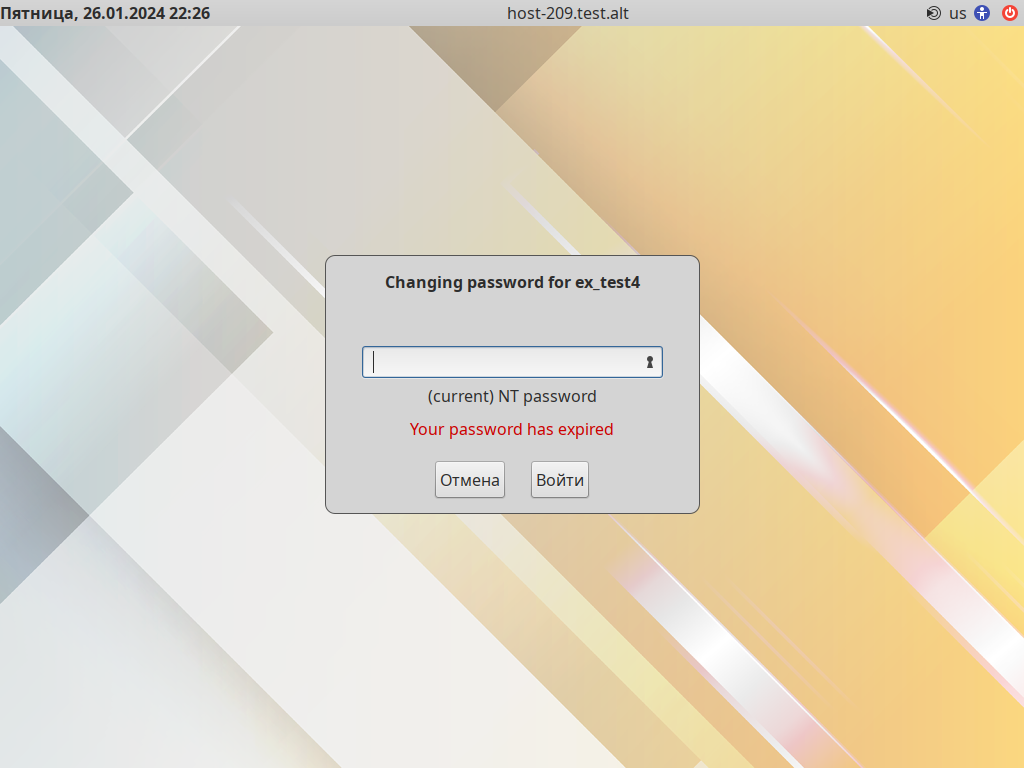
Порядок смены пароля в lightdm
После ввода имени доменного пользователя и его текущего домена ему будет предложено заменить пароль, указав повторно текущий пароль:
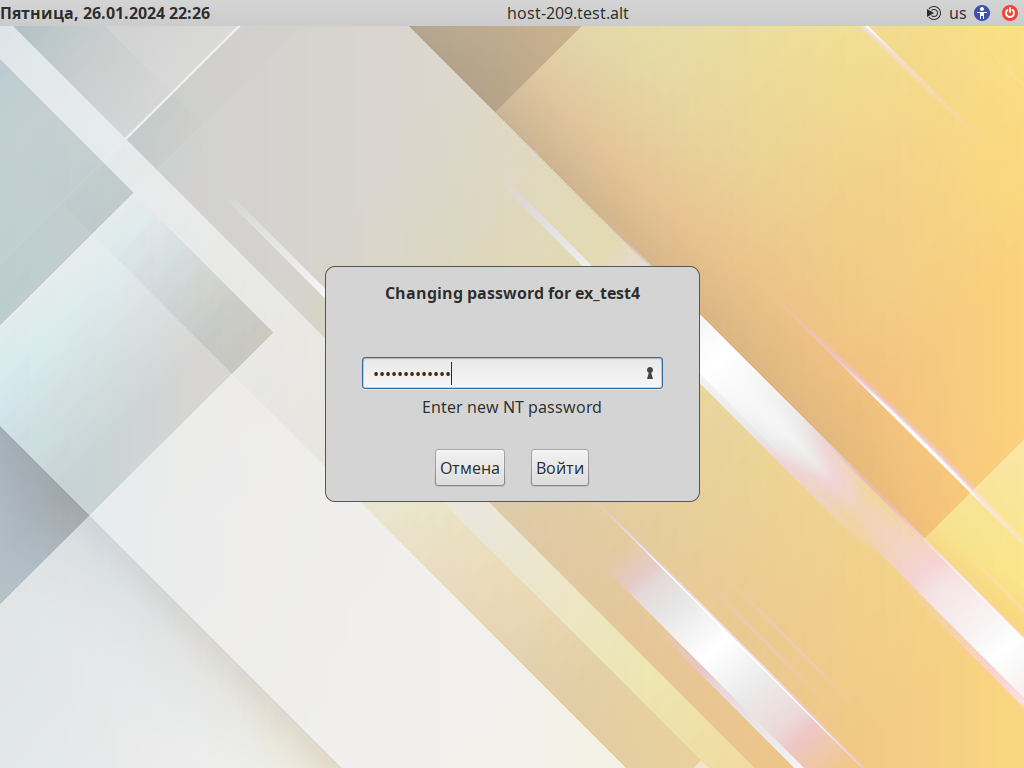
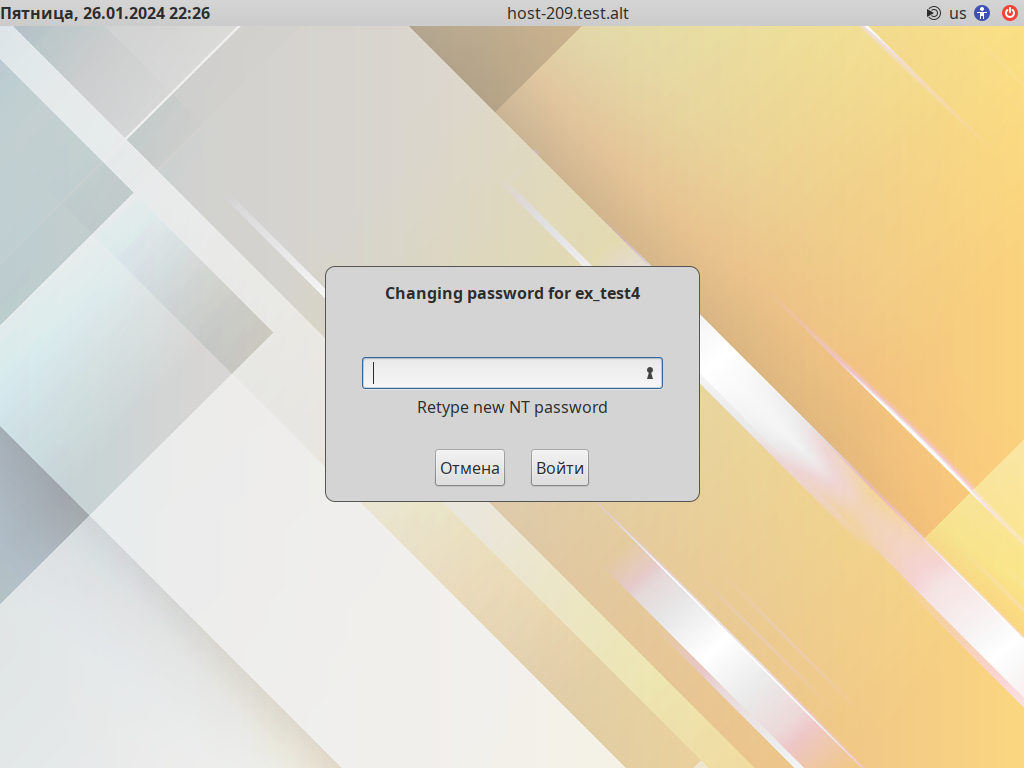
Затем дважды укажите новый пароль. Он не должен совпадать с последними паролями этого пользователя.
Журнал входа
# journalctl -g pam_winbind | cut -f4- -d:
-- Boot aca50047241941a795b4743e27407d72 --
pam_winbind(lightdm:auth): [pamh: 0x55b8cfc0db80] ENTER: pam_sm_authenticate (flags: 0x0000)
pam_winbind(lightdm:auth): getting password (0x00010381)
pam_winbind(lightdm:auth): Verify user 'ex_test4'
pam_winbind(lightdm:auth): CONFIG file: krb5_ccache_type 'KEYRING'
pam_winbind(lightdm:auth): enabling krb5 login flag
pam_winbind(lightdm:auth): enabling cached login flag
pam_winbind(lightdm:auth): enabling request for a KEYRING krb5 ccache
pam_winbind(lightdm:auth): request wbcLogonUser failed: WBC_ERR_AUTH_ERROR, PAM error: PAM_AUTHTOK_EXPIRED (27), NTSTATUS: NT_STATUS_PASSWORD_EXPIRED, Error message was: The user account password has expired.
pam_winbind(lightdm:auth): user 'ex_test4' password expired
pam_winbind(lightdm:auth): [pamh: 0x55b8cfc0db80] LEAVE: pam_sm_authenticate returning 0 (PAM_SUCCESS)
pam_winbind(lightdm:account): [pamh: 0x55b8cfc0db80] ENTER: pam_sm_acct_mgmt (flags: 0x0000)
pam_winbind(lightdm:account): pam_sm_acct_mgmt success but PAM_WINBIND_NEW_AUTHTOK_REQD is set
pam_winbind(lightdm:account): user 'ex_test4' needs new password
pam_winbind(lightdm:account): [pamh: 0x55b8cfc0db80] LEAVE: pam_sm_acct_mgmt returning 12 (PAM_NEW_AUTHTOK_REQD)
pam_winbind(lightdm:chauthtok): [pamh: 0x55b8cfc0db80] ENTER: pam_sm_chauthtok (flags: 0x4020)
pam_winbind(lightdm:chauthtok): username [ex_test4] obtained
pam_winbind(lightdm:chauthtok): getting password (0x000101a1)
pam_winbind(lightdm:chauthtok): enabling krb5 login flag
pam_winbind(lightdm:chauthtok): request wbcLogonUser failed: WBC_ERR_AUTH_ERROR, PAM error: PAM_AUTHTOK_EXPIRED (27), NTSTATUS: NT_STATUS_PASSWORD_EXPIRED, Error message was: The user account password has expired.
pam_winbind(lightdm:chauthtok): user 'ex_test4' password expired
pam_winbind(lightdm:chauthtok): [pamh: 0x55b8cfc0db80] LEAVE: pam_sm_chauthtok returning 0 (PAM_SUCCESS)
pam_winbind(lightdm:chauthtok): [pamh: 0x55b8cfc0db80] ENTER: pam_sm_chauthtok (flags: 0x2020)
pam_winbind(lightdm:chauthtok): username [ex_test4] obtained
pam_winbind(lightdm:chauthtok): getting password (0x00010181)
pam_winbind(lightdm:chauthtok): request wbcChangeUserPasswordEx succeeded
pam_winbind(lightdm:chauthtok): user 'ex_test4' OK
pam_winbind(lightdm:chauthtok): user 'ex_test4' password changed
pam_winbind(lightdm:chauthtok): CONFIG file: krb5_ccache_type 'KEYRING'
pam_winbind(lightdm:chauthtok): enabling krb5 login flag
pam_winbind(lightdm:chauthtok): enabling cached login flag
pam_winbind(lightdm:chauthtok): enabling request for a KEYRING krb5 ccache
pam_winbind(lightdm:chauthtok): request wbcLogonUser succeeded
pam_winbind(lightdm:chauthtok): user 'ex_test4' granted access
pam_winbind(lightdm:chauthtok): Returned user was 'ex_test4'
pam_winbind(lightdm:chauthtok): [pamh: 0x55b8cfc0db80] LEAVE: pam_sm_chauthtok returning 0 (PAM_SUCCESS)
pam_winbind(lightdm:setcred): [pamh: 0x55b8cfc0db80] ENTER: pam_sm_setcred (flags: 0x0002)
pam_winbind(lightdm:setcred): PAM_ESTABLISH_CRED not implemented
pam_winbind(lightdm:setcred): [pamh: 0x55b8cfc0db80] LEAVE: pam_sm_setcred returning 0 (PAM_SUCCESS)
pam_winbind(lightdm:session): [pamh: 0x55b8cfc0db80] ENTER: pam_sm_open_session (flags: 0x0000)
pam_winbind(lightdm:session): [pamh: 0x55b8cfc0db80] LEAVE: pam_sm_open_session returning 0 (PAM_SUCCESS)